Assg 02: Classes
COSC 2336 Data Structures
Objectives • Create a simple class • Practice using <cmath> math functions • Practice with C++ string types and I/O streams • Use a class constructor • Example of test driven development
Description Typically, most everyone saves money periodically for retirement. In this exercise, for simplicity, we assume that the money is put into an account that pays a fixed interest rate, and money is deposited into the account at the end of the specified period. Suppose the person saving for retirement depositsD dollarsmtimesperyear. Theaccountpaysr%compoundinterest rate. And the person will be saving for a period of t time given in years. For example, the person might save D = $500 every m = 12 months. The retirement account pays 4.8% compound interest per year. And the person as t = 25 years to save for retirement. The total amount of savings S accumulated at the end of this time is given by the formula S = Dh(1 + r/m)mt −1 r/m i For example, suppose that you deposit $500 at the end of each month (m = 12). The account pays 4.8% interest per year compounded monthly for t = 25 years. Then the total money accumulated into this account is
1
500[(1 + 0.048/12)300 −1]/(0.048/12) = 289,022.42
.
On the other hand, suppose that you want to accumulate S dollars in savings, and would like to know how much money you should deposit D each deposit period. The periodic payment you need to reach this goal S is given by the formula
D =
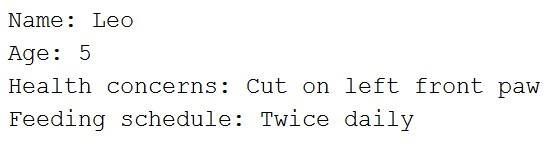
S(r/m) (1 + r/m)mt −1 Design a class that uses the above formulas to calculate retirement savings and to help plan retirement goals. Your class should have private instance variables (all of type double) to hold D the deposit amount, m the number of deposit periods per year, r the interest rate and t the time in years the plan will save for retirement. In the class style guidelines, I discourage using single letter variable names usually when writing code. However when we are directly implementing a formula in an engineering or scientific calculation, it is often clearer to use the variable names directly as given in the formula. For this assignment you need to perform the following tasks. 1. Create a class named RetirementAccount. The class should have a class constructor that takes the 4 variables, D, m, r, t as parameters. 2. Create a default class constructor as well. This constructor can set all of the private member variable values to 1.0. 3. You must have getter and setter methods for all 4 of the member variables of the class. The methods will be named set_D(), set_m(), set_r(), set_t() and get_D(), get_m(), get_r(), get_t(), respectively. 4. Create a member function named tostring(). This function will not take any parameters as input. It returns a string that represents the values/settings of the RetirementAccount class. See the example output below for the format of the string to be returned. 5. Create a member function named calculateRetirementSavings(). This function should implement the first formula to calculate the total amount of savings S the account will generate. This function has no parameters as inputs, and it returns a double amount (the amount of savings) as its result.
2
6. Create a member function named planRetirementDeposits(). This function takes a double parameters S as input, which is the savings goal you wish to achieve. This function should implement the second equation given above. The function returns a double result, D which is the amount of money that should be deposited each period to meet the savings goal S.
As before you will be given a starting template for this assignment. The template contains all of the tests your class and member functions should pass for this assignment. You should write your program by uncommenting the tests/code in main 1 at a time, and writing your class incrementally to work with the test. If you perform all of the above tasks correctly, the tests given to you in the starting template will produce the following correct output:
=== Testing class creation using constructor……………….
=== Testing getter methods………………. Account: D (deposit amount) = $100.00 m (periods per year) = 10.00 r (interest rate) = 0.0350 t (time in years) = 22.00
=== Testing tostring() method………………. Account: D (deposit amount) = $100.00 m (periods per year) = 10.00 r (interest rate) = 0.0350 t (time in years) = 22.00
=== Testing setter methods………………. Account: D (deposit amount) = $500.00 m (periods per year) = 12.00 r (interest rate) = 0.0480 t (time in years) = 25.00
=== Testing retirement savings calculations……………….
3
My retirement savings: $289022.42
=== Testing retirement planning calculations………………. In order to save 1 million dollars, we need to make monthly deposits of $1729.97 If we set our deposit to this new amount… Account: D (deposit amount) = $1729.97 m (periods per year) = 12.00 r (interest rate) = 0.0480 t (time in years) = 25.00
My retirement savings: $1000000.00
=== Second test on account2 of savings and planning………………. Account 2: D (deposit amount) = $650.00 m (periods per year) = 9.00 r (interest rate) = 0.0350 t (time in years) = 30.00
My retirement savings: $309521.45
In order to save 2 million dollars, we need to make deposits of $4200.03 If we set our deposit to this new amount… Account: D (deposit amount) = $4200.03 m (periods per year) = 9.00 r (interest rate) = 0.0350 t (time in years) = 30.00
My retirement savings: $2000000.00
=== Larger number of tests, compare effect of increasing monthly deposit amount………………. Plan 0: D (deposit amount) = $500.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 347024.70 Plan 1:
4
D (deposit amount) = $600.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 416429.64 Plan 2: D (deposit amount) = $700.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 485834.58 Plan 3: D (deposit amount) = $800.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 555239.52 Plan 4: D (deposit amount) = $900.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 624644.46 Plan 5: D (deposit amount) = $1000.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 694049.40 Plan 6: D (deposit amount) = $1100.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 763454.34 Plan 7: D (deposit amount) = $1200.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00
5
Total Savings: 832859.29 Plan 8: D (deposit amount) = $1300.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 902264.23 Plan 9: D (deposit amount) = $1400.00 m (periods per year) = 12.00 r (interest rate) = 0.0400 t (time in years) = 30.00 Total Savings: 971669.17
Hints • You can use the string type and string concatenation to write the required tostring() member function. For example, if I had variables x and y of type int and double, and I wanted to create a string from them to return, I could do something like
#include <string> using namespace std;
int x = 5; double y = 0.035 string s = “x (example int) = ” + to_string(x) + ‘\n’ + “y (example double) = ” + to_string(y) + ‘\n’; However, you cannot control the precision (number of decimal places shown)oftheoutputusingtheto_string()method. Iwillacceptthis, but if you want to get exactly the same output I showed in the correct output, you will need to use the string stream library <sstream>. This library allows you to create a stream, like the cout stream, but stream into a string. Thus you can use the io manipulator functions like setprecision() and fixed to format the decimal numbers. You can look at the starting template for many examples of using these I/O manipulators to format the output. • You should use the pow() function from <cmath> for calculating the
6
savings and planning the goal deposits functions. It might make it easier on you, and be more readable, to define something like:
// r is yearly rate, so amount if interest each period is // given by r/m double ratePerDeposit = r / m; // total number of deposits double numberOfDeposits = m * t; • Almost all of the code given in the template is commented out. You should start by only uncommenting the first line that creates an object using your constructor, this one:
// RetirementAccount account(100.00, 10.0, 0.035, 22.0); Get your constructor working first for your class. Then you should uncomment out the first line testing the get_D() getter method, etc. E.g. if you are not used to coding incrementally, try it out. Code only a single function and get it working before doing the next one. This is a type of test driven development.
Assignment Submission A MyLeoOnline submission folder has been created for this assignment. You should attach and upload your completed .cpp source file to the submission folder to complete this assignment.
Requirements and Grading Rubrics Program Execution, Output and Functional Requirements 1. Your program must compile, run and produce some sort of output to be graded. 0 if not satisfied. 2. 25 pts. The class must have the requested member variables. These member variables must be private. 3. 25 pts. The constructor is created and working correctly. 4. 10 pts. All setter and getter methods for the 4 member variables are implemented and work as asked for.
7
5. 10pts. YouhavecorrectlyimplementedthecalculateRetirementSavings() function, and it is calculating savings correctly. 6. 10pts. YouhavecorrectlyimplementedtheplanRetirementDeposits() function, and it it calculating goal deposits correctly. 7. 10 pts. You have correctly implemented the tostring() method. The method is returning a string (not sending directly to cout). 8. 2 pts. (bonus) You used <sstream> string streams, and have correctly formatted the string to have 2 or 4 decimal places as shown in correct output. 9. 5 pts. All output is correct and matches the correct example output. 10. 5pts. Followedclassstyleguidelines, especiallythosementionedbelow.
Program Style Your programs must conform to the style and formatting guidelines given for this class. The following is a list of the guidelines that are required for the assignment to be submitted this week.
1. Mostimportantly, makesureyoufigureouthowtosetyourindentation settings correctly. All programs must use 2 spaces for all indentation levels, and all indentation levels must be correctly indented. Also all tabsmustberemovedfromfiles,andonly2spacesusedforindentation. 2. A function header must be present for member functions you define. You must give a short description of the function, and document all of the input parameters to the function, as well as the return value and data type of the function if it returns a value for the member functions, just like for regular functions. However, setter and getter methods do not require function headers. 3. You should have a document header for your class. The class header document should give a description of the class. Also you should document all private member variables that the class manages in the class document header. 4. Do not include any statements (such as system(“pause”) or inputting a key from the user to continue) that are meant to keep the terminal from going away. Do not include any code that is specific to a single
8
operating system, such as the system(“pause”) which is Microsoft Windows specific.
(File need to be in ‘.cpp’. Use any C++ compilers but the code must be working.

 OR
OR 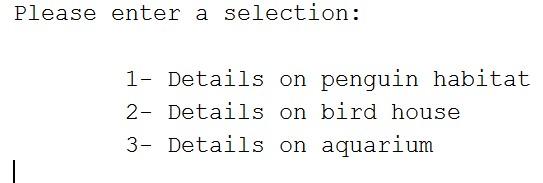
 OR
OR